Enhanced Mutual Authentication Scheme for Fog Computing using Blockchain Technology
DOI:
https://doi.org/10.37934/ard.141.1.163188Keywords:
Fog computing, cloud computing, mutual authentication, blockchainAbstract
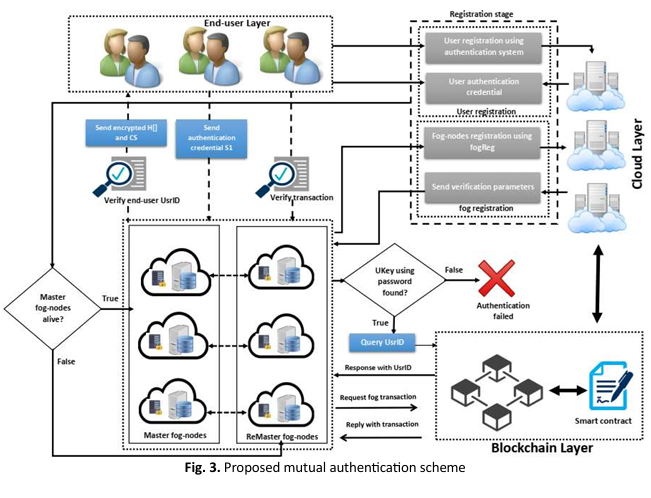
Fog computing is an innovative concept that extends cloud services further and brings their capabilities even closer to end-users by extending them out as far as the network edge. Since edges operate on resources that are closer to the source of data, this goes a process in addressing some of the problems with traditional cloud computing - especially latency. Unfortunately, while this proposal offers some benefits it does not by itself ensure that edge devices are trustworthy or behaving securely. As a result, security continues to be one of the key focus points in fog computing deployment. In this context, authentication is an essential component of any security system. Traditional authentication systems do not work well in the fog computing context; therefore, an efficient mutual i.e. two-way authentication process should be used between edge devices and fog servers because of the low end-to-end latency constraints. This paper proposes an improved mutual authentication scheme specifically designed for fog computing environments to overcome these struggles. Our proposal scheme ensures mutual verification between fog servers and edge devices can effectively strengthen security against potential threats. It makes sure there is very low to no storage overhead on fog servers which increases efficiency, especially in resource-constrained environments. Our scheme is tested through extensive experiments and mathematical analysis.
Downloads